Is Zscaler a VPN and Whats the Difference? A Clear Guide to Zscaler, VPNs, and Safe Online Browsing
Is Zscaler a VPN and Whats the Difference? In short: no, Zscaler isn’t a traditional VPN, and the way it handles security and traffic is different from a typical VPN. Here’s a practical, up-to-date guide to help you understand where Zscaler fits in, how it compares to VPNs, and when you should use each.
Quick fact: Zscaler is a cloud-based secure access service edge SASE platform that focuses on zero-trust security, secure web gateway, and cloud firewall capabilities rather than just masking your IP like a classic VPN.
Useful resources to check out as you read:
- Apple Website - apple.com
- Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence
- Zscaler official - zscaler.com
- VPN comparison guides - en.wikipedia.org/wiki/Virtual_private_network
- Cybersecurity best practices - csoonline.com
Introduction: Is Zscaler a VPN and Whats the Difference? A quick, practical overview
- Is Zscaler a VPN? No. It’s not a traditional VPN that merely tunnels your traffic to a remote server. Zscaler operates as a cloud-based security platform that can enforce Zero Trust Network Access ZTNA, secure web gateway, data loss prevention, and firewall-as-a-service. It sits between users and the internet, inspecting traffic to protect data and enforce policies.
- Why this matters: If you mainly want to hide your IP for geoblocking or access region-restricted content, a VPN is the more straightforward tool. If your goal is corporate-grade security—authenticating users, controlling apps, and inspecting traffic—Zscaler’s model is often preferable.
- Quick path to understanding:
- VPNs create a private tunnel between you and a server and often route all traffic through that tunnel.
- Zscaler sits in the cloud and applies security policies to traffic, regardless of where you’re located, often without forcing all traffic to a single exit point.
- Zscaler can work with or without remote access VPNs to provide secure access to apps, websites, and services.
- Real-world takeaway: If your company already relies on Zscaler for security, you’ll get strong protection and policy enforcement, but you may still use a VPN in some scenarios for privacy or remote access to specific networks.
- Quick-start tips:
- For personal privacy and bypassing geo-restrictions, consider a reputable VPN with a strict no-logs policy.
- For protecting corporate data and enforcing access controls, rely on Zscaler’s SASE/ZTNA features.
- If you’re unsure what your organization uses, check with your IT department or security admin.
What Zscaler Actually Does and Why It Matters
- Core components:
- Zscaler Internet Access ZIA: A secure web gateway that inspects and filters all user traffic to the internet, blocking threats and enforcing policies.
- Zscaler Private Access ZPA: A zero-trust VPN alternative that provides seamless, policy-based access to internal apps without exposing the network.
- Zscaler Cloud Firewall: A centralized firewall-as-a-service that applies traffic rules regardless of user location.
- Data loss prevention DLP and SSL inspection to detect sensitive data leaks and threats inside encrypted traffic.
- How it works in practice:
- When you sign in, traffic is redirected to Zscaler’s cloud services via a lightweight client or browser extension, depending on deployment where it’s scanned, authenticated, and then routed to its destination if allowed.
- This approach reduces the need for backhauls to corporate networks, speeding up access to cloud apps while maintaining security posture.
- Key benefits:
- Strong zero-trust security: authentication and least-privilege access for users and devices.
- Consistent security posture across endpoints and locations, including remote work.
- Simplified management: policy, enforcement, and visibility centralized in the cloud.
- Potential drawbacks to know:
- Some users report occasional latency when traffic inspection adds processing time depends on location, policy, and network conditions.
- For simple privacy concerns, a VPN may feel more straightforward because it masks IP but doesn’t inherently enforce organization-wide security policies.
- Use cases:
- Enterprises needing secure remote access to internal apps without exposing the network.
- Organizations wanting to replace traditional perimeters with a Zero Trust model.
- Scenarios requiring centralized policy enforcement and threat protection across cloud and on-prem resources.
VPNs vs. Zscaler: A Side-by-Side Look at Core Differences
- Purpose:
- VPN: Primarily to hide your IP, mask your location, and provide a private tunnel to a remote network or server.
- Zscaler: Primarily to secure user traffic, enforce security policies, and provide zero-trust access to apps and the internet.
- Traffic flow:
- VPN: Routes most or all traffic through a VPN server remote exit point. You appear as if you’re in the VPN server’s location.
- Zscaler: Routes traffic to the nearest Zscaler cloud service for inspection, policy enforcement, and then to the destination no single exit point for all traffic.
- Security model:
- VPN: Focused on confidentiality and access to a private network.
- Zscaler: Focused on security, threat prevention, and access control across the internet and private apps, via zero-trust principles.
- Ideal use cases:
- VPN: Personal privacy, geobypass for streaming note: this may violate terms of service for some platforms, secure remote access to a company network via a dedicated VPN.
- Zscaler: Corporate security, secure access to apps, compliance with data protection rules, and threat prevention for all internet-bound traffic.
- Performance considerations:
- VPN: Some slowdown due to encryption and distance to VPN exit servers; performance highly depends on server location and ISP.
- Zscaler: Latency depends on your location relative to Zscaler data centers and policy complexity; generally optimized for cloud-first access but can add inspection overhead.
- Privacy implications:
- VPN: Masks your IP, but your VPN provider can see your traffic unless you use strong privacy policies and avoid logging.
- Zscaler: Primarily a security tool for enterprises; not designed for anonymous browsing. It logs traffic for security and policy enforcement, subject to company and legal policies.
How to Decide: Do You Need a VPN, Zscaler, or Both?
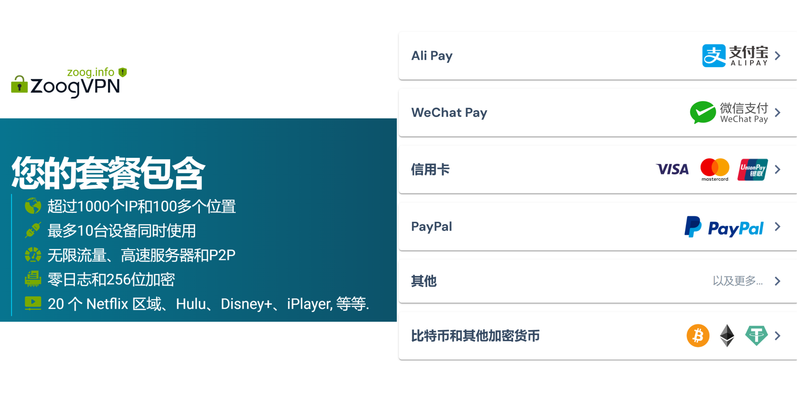
- If your goal is to privately browse the web or bypass geoblocks for streaming, a consumer VPN is typically the simpler route. Look for a provider with:
- A clear no-logs policy
- Strong encryption AES-256
- Fast and diverse server locations
- Transparent ownership and independent audits
- If you’re part of an organization using Zscaler, you’ll benefit from enterprise-grade security and app access control. In this case:
- Expect policy-driven access to apps
- Traffic inspection and threat prevention across cloud and internet traffic
- Centralized management by your IT/security team
- If you’re balancing both: you might use Zscaler for work-related browsing and app access, and a personal VPN for privacy-focused activities on non-work devices. Coordinate with your IT team to avoid conflicts or double filtering.
Real-World Scenarios and Examples
- Scenario A: Remote worker accessing internal HR apps
- Zscaler ZPA enables secure, zero-trust access to internal applications without exposing the whole network. No need for a traditional VPN tunnel to the corporate network.
- Scenario B: You want to stream from a country-restricted service
- A consumer VPN can help you appear in a different location, provided its terms of service allow it. Remember, streaming platforms often crack down on VPNs.
- Scenario C: You’re concerned about security on public Wi-Fi
- Zscaler’s threat protection helps, but you can combine with a privacy-minded VPN for extra anonymity. Ensure you understand policy implications and device security settings.
Implementation Considerations: Getting Started with Zscaler for Organizations
- Deployment options:
- ZIA for internet traffic protection web filtering, malware protection, SSL inspection.
- ZPA for private app access without exposing the network.
- Typical rollout steps:
- Baseline security policy and zero-trust framework
- User and device enrollment
- Traffic redirection to Zscaler cloud
- Continuous monitoring and policy updates
- Common pitfalls:
- Overly aggressive SSL inspection can cause compatibility issues with some apps
- Latency concerns if not properly distributed across regions
- Metrics to track:
- Threat detections per user/device
- Access success rates to sanctioned apps
- VPN replacement rate for ZPA coverage
Technical Deep Dive: How Zscaler Works Behind the Scenes
- Zero Trust Architecture:
- Every access request is verified, regardless of user location
- Access is granted only to specific apps or resources, not to the entire network
- Cloud-based inspection:
- Traffic is decrypted for inspection where allowed and re-encrypted before reaching the destination
- DLP and malware protection operate across web, cloud apps, and internal resources
- Policy management:
- Central policies control who can access what, from where, and on which devices
- Automated updates keep security postures current
Security and Privacy Considerations
- Data handling:
- Zscaler processes traffic to enforce security; this can involve logging for compliance and security monitoring.
- Understand your organization’s data retention and privacy policies.
- Compliance:
- Zscaler supports various compliance frameworks e.g., GDPR, HIPAA, etc. when configured properly.
- Personal use cautions:
- If you’re using Zscaler in a corporate context, don’t bypass security controls or attempt to sidestep policy settings. It can violate company policy and law.
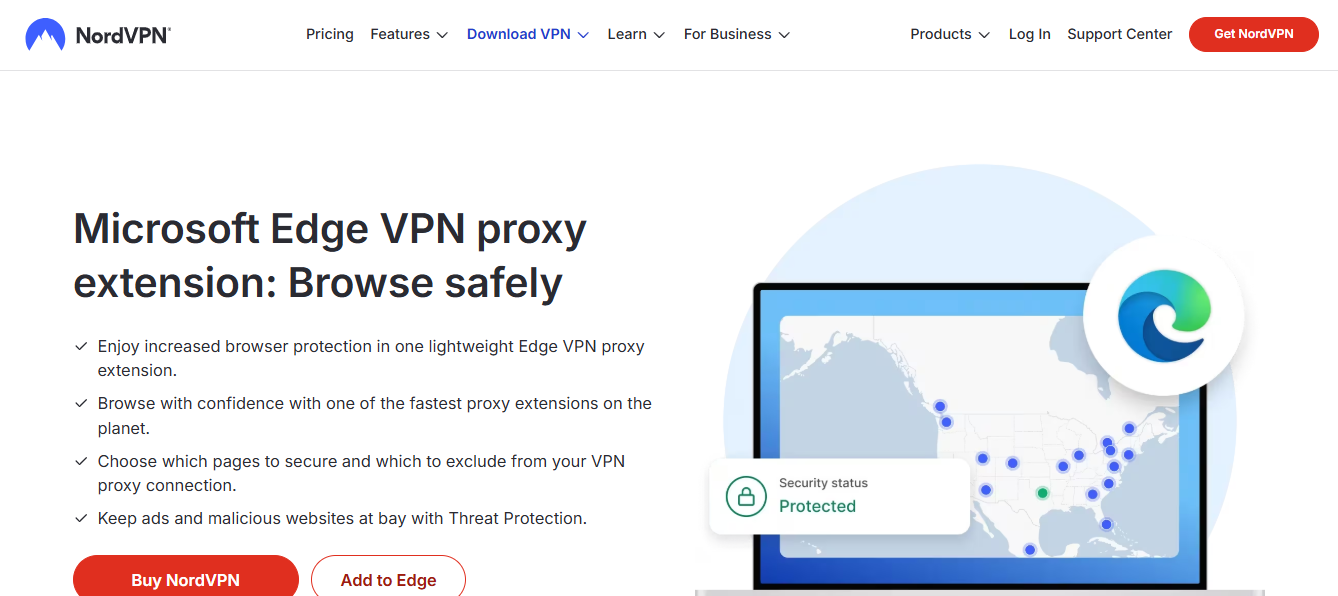
How to Choose a VPN in the Era of Zscaler
- Key features to look for in a VPN today:
- Strong encryption AES-256, secure tunneling protocols WireGuard, OpenVPN, IKEv2
- No-logs policy and independent audits
- Fast, diverse server network and good performance
- Clear privacy policy and jurisdiction transparency
- When to pair with Zscaler:
- If you want both corporate security and personal online privacy, you can use a VPN on non-work devices or in personal contexts, while your work traffic is routed through Zscaler for security.
Common Misconceptions About Zscaler and VPNs
- Misconception: Zscaler is just a VPN.
- Reality: It provides secure access and threat protection with a zero-trust approach, not just tunneling like a VPN.
- Misconception: Using Zscaler means you lose all privacy.
- Reality: Zscaler is designed for security and policy enforcement; it logs for security and auditing, which is standard in enterprise environments.
- Misconception: A VPN always slows you down.
- Reality: VPN performance depends on server load, distance, and provider optimization; modern VPNs can be fast, but Zscaler’s cloud inspection can add some overhead.
Best Practices for Users
- For personal use:
- Choose a reputable VPN with a clear privacy policy, fast servers, and robust encryption.
- Use two-factor authentication 2FA on your accounts and keep software updated.
- For corporate use:
- Follow IT guidelines for ZPA/ZIA deployment
- Report issues like latency or app incompatibilities to IT
- Regularly review access permissions and policy updates
Recommended Setup Guide Step-by-Step
- Step 1: Assess your needs
- Are you protecting corporate data, or just browsing privately?
- Step 2: Choose your tools
- If corporate, align with Zscaler products; if personal, pick a trusted VPN.
- Step 3: Deployment or installation
- Follow vendor guides for Zscaler deployment in a business environment.
- For VPN, install the client on your devices and log in with your credentials.
- Step 4: Configure policies and preferences
- Set secure defaults, enable 2FA, and tailor access rules as needed.
- Step 5: Test and monitor
- Verify access to required apps, check for any blocked content, and monitor performance.
- Step 6: Ongoing maintenance
- Keep software updated, review security reports, and adjust policies as needed.
FAQ Section
Frequently Asked Questions
Is Zscaler a VPN?
No, Zscaler is not a traditional VPN. It’s a cloud-based security platform that provides zero-trust access, secure web gateway, and firewall capabilities, often replacing or augmenting VPN connections for enterprise setups.
What is ZPA in Zscaler?
Zscaler Private Access ZPA is Zscaler’s solution for zero-trust access to internal apps without exposing the entire network. It replaces classic VPNs for remote access to applications.
How does ZIA differ from a VPN?
ZIA Zscaler Internet Access is a secure web gateway that inspects and protects traffic heading to the internet. It doesn’t simply tunnel your traffic; it enforces security policies and blocks threats.
Can Zscaler replace my VPN entirely?
In many enterprise scenarios, yes. Zscaler can replace traditional VPNs for remote app access and secure browsing, though some organizations may still use VPNs in certain cases depending on requirements.
Is Zscaler private or public?
Zscaler is a cloud-based service that operates in the public cloud but is managed by Zscaler and integrated with your organization’s security policies. Windscribe vpn extension for microsoft edge a complete guide 2026: Comprehensive setup, tips, and comparisons
Does Zscaler log user traffic?
Yes, for security, compliance, and policy enforcement. Logging policies are defined by the organization and applicable laws.
Will Zscaler slow down my internet?
There may be some latency due to traffic inspection and policy enforcement, but the impact varies by location and policy complexity. Most users experience acceptable performance, especially for modern cloud apps.
Can I use Zscaler on my personal device?
Zscaler is typically deployed by organizations for employees. Personal usage is rare, but some individuals may access a company’s Zscaler-enabled environment if permitted by their employer.
How do I know if my company uses Zscaler?
Ask your IT department or security team, or look for a lightweight client or browser extension that routes traffic through Zscaler.
Is a VPN illegal to use with Zscaler?
Using a VPN with Zscaler isn’t illegal, but it could conflict with corporate policies. Always check your organization’s guidelines before combining security tools. Cant connect to work vpn heres how to fix it finally
How do I optimize Zscaler performance?
- Ensure you’re on a stable internet connection
- Use devices that meet minimum security requirements
- Avoid unnecessary SSL inspection flags by adjusting allowed apps
- Work with IT to ensure optimal regional data center routing
Is Zscaler a VPN and Whats the Difference? Final Thoughts
- In the real world, Zscaler is not a VPN. It’s a security-first platform designed to protect users and apps across the internet and private resources, using zero-trust principles and cloud-native protection. If you’re shopping for privacy and the ability to appear from a different location, a consumer VPN is your friend. If you’re a business looking to secure access to internal apps without broad network exposure, Zscaler is a powerful, scalable choice.
- For individuals juggling both privacy and corporate security, coordinate with your IT team to understand what’s best in your environment. And if you’re curious about privacy-friendly, independent VPN options, check out trusted providers with clear policies and strong encryption.
Endnotes and Additional Resources
- Zscaler official: zscaler.com
- VPN literacy and comparisons: en.wikipedia.org/wiki/Virtual_private_network
- Secure web gateway concepts: cisco.com/c/en/us/products/security/security-architectures/security-fundamentals/security-fundamentals-vpn-vguard.html
- Zero Trust security principles: csoonline.com/article/3246338/what-is-zero-trust-security-exactly.html
- Privacy-focused best practices: electronic frontier foundation - eff.org
If you want, I can tailor this draft to align with specific video parts, timestamps, or chapters for a YouTube video script.
Sources:
5 Best VPNs for Xcloud Bypass Geo Restrictions Get the Lowest Possible Ping
辰民爸爸 esim:告别实体卡,畅享全球无忧上网新体验:VPN 使用教程、隐私保护与跨境上网策略 Microsoft edge vpn mit jamf und conditional access policy in osterreich ein umfassender leitfaden
Nordlynx no internet fix connection issues get back online: Quick Guide, Real Fixes, and Pro Tips
How to use nordvpn openvpn config files your complete guide
Vpn未识别的网络:完整指南与实用技巧