Is Using a VPN with Citrix Workspace a Good Idea Lets Talk Safety and Performance
Is using a vpn with citrix workspace a good idea lets talk safety and performance. Quick fact: VPNs can add a layer of security and privacy, but they can also affect latency and application performance, especially with enterprise-grade tools like Citrix Workspace. This guide breaks down how VPNs interact with Citrix, plus practical steps, best practices, and real-world tips so you can decide what works for your organization.
- What you’ll learn:
- How VPNs affect Citrix Workspace performance and security
- The best VPN types and configurations for enterprise use
- Step-by-step setup tips, common pitfalls, and troubleshooting
- Data privacy, compliance, and threat considerations
- A practical checklist to decide if a VPN is right for your Citrix environment
Useful resources you might want to check later text only, unclickable: Apple Website - apple.com Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence Citrix Official - citrix.com VPN Security Guide - nist.gov NordVPN - nordvpn.com
Introduction: quick facts and what to expect Youtube Premium with VPN Not Working Here’s How to Fix It Fast
- VPNs can mask user identity and encrypt traffic, which is great for privacy and securing data in transit.
- Citrix Workspace is designed for remote access, performance, and secure application delivery, but it’s sensitive to network quality and routing.
- The moment you introduce a VPN, you add an extra hop, potential packet loss, and jitter, which can impact login times, app responsiveness, and virtual desk performance.
- The right VPN setup can reduce risk and meet compliance needs; the wrong setup can degrade user experience and complicate IT monitoring.
In this post, we’ll cover:
- The basics: what a VPN does and how Citrix Workspace uses the network
- Real-world implications: latency, bandwidth, and connection stability
- VPN types that fit Citrix environments and why
- Configuration best practices: split tunneling, DNS, MTU, and more
- Security and compliance considerations
- Step-by-step setup tips for a smooth deployment
- Troubleshooting common issues
- A practical decision-making checklist for your organization
- FAQs to clear up common doubts
What is Citrix Workspace and why add a VPN?
- Citrix Workspace delivers virtual apps and desktops to end users, often over the public internet or private networks.
- A VPN creates an encrypted tunnel between the user device and the corporate network, protecting data in transit and often enabling access to internal resources.
- When combined, you get improved privacy and access control, but with potential performance bumps that must be managed.
Key terms you’ll hear a lot
- VPN: Virtual Private Network, encrypts traffic and routes it through a secure server.
- Split tunneling: A VPN feature allowing only some traffic to go through the VPN, while the rest uses the regular internet.
- MTU: Maximum Transmission Unit, the largest packet size that can be transmitted without fragmentation.
- Jitter: Variability in packet arrival times, which can affect real-time apps.
- Throughput: The amount of data transferred in a given time period.
How VPNs impact Citrix Workspace: performance, security, and reliability
- Latency and jitter: Each extra network hop can add latency. Citrix is sensitive to latency because it relies on real-time updates for a smooth user experience.
- Throughput: VPN encryption overhead reduces raw bandwidth. In busy environments, this can show up as slower logins and slower app performance.
- Consistency: VPNs can introduce routing changes or variability if the VPN service shifts servers or experiences outages.
- Security: VPNs add encryption and can enforce access controls, reducing exposure to insecure networks public Wi‑Fi, etc..
- Visibility and monitoring: VPNs can hide some traffic from standard IDS/IPS or VPN logs may complicate troubleshooting if IT isn’t centralized.
Which VPN types work best with Citrix? Configurer un serveur vpn sur qnap pour securiser lacces a vos donnees via microsoft edge: Guide complet et optimisé
- Site-to-site VPNs branch office to data center: Good for centralized Citrix deployments where users are on managed devices. Provides stable tunnels but can be heavy on gateways.
- Client-based VPNs endpoint VPN: Common for remote users. Offers strong security but requires careful QoS and client configuration to avoid performance hits.
- SD-WAN with VPN overlay: Combines optimization with secure transport. Great for distributed deployments; can improve performance by choosing optimal paths.
- Per-app VPN mobile/remote gateways: Useful for mobile Citrix access where you only route specific apps or data through the VPN.
Best practices for Citrix + VPN deployments
- Use split tunneling where appropriate
- Pros: Reduces VPN load, improves performance for non-Citrix traffic.
- Cons: Potential security gaps if not configured properly; ensure corporate resources still protected.
- Optimize for Citrix traffic
- Route only Citrix related traffic through VPN when necessary; otherwise, use direct internet for non-critical traffic.
- DNS considerations
- Ensure DNS resolution works both inside and outside VPN. Split DNS can help avoid leaks and ensure internal resources resolve correctly.
- MTU and fragmentation
- Start with MTU 1400–1472 range for UDP-based Citrix traffic. Adjust based on path MTU findings to minimize fragmentation.
- Quality of Service QoS
- Prioritize Citrix traffic over VPN tunnels. Use DSCP markings or router/switch QoS features to protect latency-sensitive flows.
- Authentication and access controls
- Implement MFA for VPN access and integrate with Citrix Access Control if possible.
- Certificate hygiene
- Use valid certificates for VPN gateways and ensure device trust is maintained across endpoints.
- Logging and monitoring
- Centralize VPN logs with Citrix analytics or your SIEM. Monitor login times, tunnel health, and anomaly events.
- Redundancy and failover
- Plan for VPN gateway redundancy and Citrix delivery controller failover. Test failover scenarios regularly.
Step-by-step setup guide high level
- Assess requirements
- Number of remote users, locations, devices, and compliance needs.
- Determine whether split tunneling is appropriate, and which resources must be accessed via VPN.
- Choose the right VPN topology
- Decide between client-based VPN, site-to-site, or SD-WAN overlay based on organization size and needs.
- Prepare Citrix environment
- Ensure NetScaler/VPN integration if using Citrix Gateway, configure delivery groups, and verify internal resource accessibility.
- Configure the VPN
- Set MTU, enable split tunneling if chosen, implement MFA, and enforce device posture checks.
- DNS and WINS configuration
- Configure split DNS for internal resource hostname resolution.
- QoS and routing
- Implement QoS rules to protect Citrix traffic, verify routing tables, and test latency under load.
- Pilot testing
- Run a pilot with a small user group, measure login times, session stability, and application responsiveness.
- Rollout
- Gradual rollout with ongoing performance monitoring and feedback loops.
- Ongoing optimization
- Regularly review VPN load, update encryption settings if needed, and adjust QoS as user patterns change.
Security considerations: risks and mitigations
- Data in transit is protected, but endpoints can still be vulnerable. Use endpoint security solutions and strict device posture checks.
- VPN fatigue: users may disable VPN or leave devices unmanaged. Enforce compliance policies and MFA to reduce risk.
- Insider risk: VPN access can grant broad internal access. Use granular access controls, just-in-time access, and session logging.
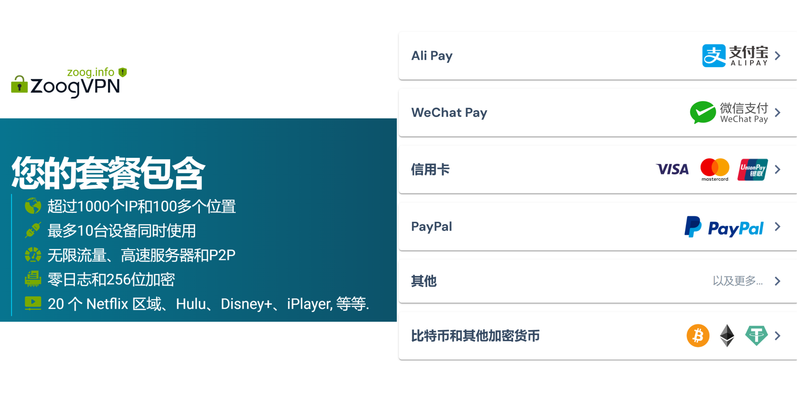
- Vendor risk: If using public VPN services, review their privacy policy, logs retention, and audit reports.
- Compliance alignment: Ensure the VPN approach aligns with data protection standards relevant to your industry e.g., GDPR, HIPAA, PCI-DSS.
Performance optimization tips
- Prefer SD-WAN or VPN overlay solutions with application-aware routing to optimize Citrix traffic paths.
- Use local breakouts where possible to minimize the distance data travels.
- Regularly test network speed, jitter, and packet loss at different times of day to identify bottlenecks.
- Consider Citrix Gateway formerly NetScaler Gateway for integrated secure access with performance optimizations.
- Monitor VPN latency separately from Citrix performance metrics to isolate issues.
Real-world data and benchmarks Google chrome not working with nordvpn heres what you need to fix it
- In enterprise studies, VPN overhead can range from 5% to 25% additional latency depending on encryption, path length, and server load.
- Citrix session startup times can be impacted by DNS resolution and RTT round-trip time to the Citrix gateway, so optimizing DNS and nearest gateway selection matters.
- SD-WAN deployments with VPN overlays can reduce overall latency by 15–40% in distributed setups due to better path selection and WAN optimization.
Tools and resources to help
- Citrix Gateway and Citrix Analytics for integrated visibility
- Your VPN provider’s analytics and tunnel health dashboards
- SIEM and endpoint protection for comprehensive security monitoring
- Network performance monitoring tools to track latency, jitter, and packet loss
Common pitfalls to avoid
- Overloading VPN gateways during peak hours without scaling
- Not validating DNS resolution in VPN and split-DNS setups
- Skipping MFA or device posture checks for VPN access
- Failing to plan for failover and disaster recovery in VPN topology
- Underestimating the impact of MTU and fragmentation on Citrix sessions
A practical decision checklist
- Do you need to extend corporate resources securely to remote workers? If yes, a VPN is useful.
- Can you tolerate some added latency for enhanced security? If performance is mission-critical, optimize rather than skip VPN.
- Is split tunneling appropriate for your risk profile? If not, route all traffic through VPN but prepare for bandwidth needs.
- Do you have MFA and device posture checks in place? If not, add them before rolling out.
- Is your Citrix Gateway integrated with your VPN for unified access control? If not, consider a consolidated solution.
- Do you have monitoring in place to correlate VPN and Citrix performance? If not, implement dashboards and alerting.
- Will you test this with a pilot group first? Always yes.
- Do you have redundancy in VPN gateways and Citrix delivery controllers? Yes? Great. If not, plan it.
Comparison: VPN types in practice quick table
- Client-based VPN
- Pros: Strong security, easy remote access
- Cons: Potential performance hit, client configuration complexity
- Site-to-site VPN
- Pros: Stable for branches, centralized control
- Cons: Requires gateway capacity, not ideal for roaming users
- SD-WAN with VPN overlay
- Pros: Best path selection, optimized performance, scalable
- Cons: Higher deployment cost, more complex management
- Per-app VPN
- Pros: Focused security for mobile apps
- Cons: Limited scope, may not cover all Citrix resources
Observations and tips for teams How to Install ExpressVPN on Linux Your Step by Step Guide
- Start with a clear policy: which traffic goes through VPN, which does not, and why.
- Use Citrix Gateway as a central access point when possible to unify access and security controls.
- Keep VPN client software up to date and educate users on proper usage during onboarding.
- Engage your network team early to validate paths, MTU, and QoS settings before rollout.
- Plan for scaling: growth in remote work means VPN capacity needs to scale with user demand.
Frequently asked questions
Is a VPN required for Citrix Workspace access?
A VPN is not always required for Citrix Workspace access, but it’s commonly used to protect data in transit and enforce corporate access policies. Alternatives include Citrix Gateway with zero-trust principles or direct secure access via cloud-delivered services.
What are the main risks of using a VPN with Citrix?
Key risks include added latency, potential routing issues, VPN server bottlenecks, and challenges with monitoring. Proper sizing, QoS, and monitoring mitigate these risks.
How does split tunneling affect security?
Split tunneling can reduce VPN load and improve performance but may increase exposure to unsecured networks. Use strict access controls and DNS segmentation to minimize risk.
How can I reduce Citrix login times when VPN is enabled?
Improve by reducing network hops choose nearest gateway, enabling split tunneling for non-Citrix traffic, tuning MTU, and ensuring MFA prompts are efficient. How to Change NordVPN Language to English Easy Steps: Quick Guide, Tips, and Alternatives
Which VPN protocols are best for Citrix?
UDP-based protocols like OpenVPN UDP, WireGuard, or IPsec with modern configurations generally perform well. The exact choice depends on your environment and compliance needs.
Should I use SD-WAN with VPN for Citrix?
If you have a distributed workforce and multiple sites, SD-WAN with VPN overlay often yields better performance and reliability.
How do I measure VPN impact on Citrix performance?
Track login times, session startup, screen refresh rate, latency to the Citrix gateway, and user-reported experience. Use end-to-end monitoring dashboards.
Can VPNs help with regulatory compliance?
Yes, VPNs can help with data-in-transit protection and access controls, but you must design with proper data handling, logging, and retention policies to meet specific regulations.
What about mobile users and VPNs?
Per-app or full VPNs can be used, but you should balance battery life and performance. Consider VPN solutions that offer background operation with minimal impact. Best nordvpn extension for microsoft edge browser in 2026: Tips, Setup, and Why It Matters
Conclusion note Is using a vpn with citrix workspace a good idea lets talk safety and performance? The answer is nuanced: a VPN can significantly boost security and control, but it introduces performance considerations that must be managed with careful configuration, monitoring, and ongoing optimization. By following the best practices above, you can achieve a secure, reliable Citrix experience for your remote workforce.
Appendix: quick resource list
- Citrix Gateway configuration guides
- VPN vendor documentation for enterprise deployments
- Network performance benchmarks for Citrix over VPN
- Compliance standards relevant to your industry
- MFA and device posture best practices
Frequently Asked Questions continued
How can I test VPN performance before full rollout?
Run a pilot with representative users, simulate peak load, and collect metrics on login times, session stability, and application responsiveness. Use synthetic tests and real user feedback.
What is the best way to implement VPN for a hybrid Citrix environment?
Use a hybrid approach with SD-WAN for performance, Citrix Gateway for secure access control, and split tunneling where appropriate to balance security and performance. Unlocking nordvpn for free the real deals and what to watch out for
Can I replace a VPN with direct secure access to Citrix resources?
In some cases yes, using zero-trust network access ZTNA or cloud-delivered secure access can reduce the need for traditional VPNs while maintaining security and access controls.
How do I ensure DNS works correctly with VPN?
Configure split DNS so internal resources resolve to internal IPs when connected via VPN, and ensure external DNS resolves public resources normally.
Are there any licensing considerations when using VPN with Citrix?
Licensing typically depends on your VPN solution and Citrix deployment. Confirm with your vendors about concurrent connections, gateway capacity, and performance-based licensing.
Sources:
Best vpn for emby keep your media server secure and private: Essential Guide for 2026
Surfshark 可以看 netflix 吗?2025 最新实测与教程,解锁全球影库 Astrill vpn fonctionne en chine la seule astuce qui marche vraiment en 2026 et autres solutions VPN de confiance
How to Add Electric Start to Your Outboard Motor: A Complete DIY Guide 2026
Vpn 机场推荐:完整攻略與實用清單,深入比較與實測
Connecting to your remote desktop with nordvpn your ultimate guide: fast, secure, and simple