Aws vpn wont connect your step by step troubleshooting guide: Quick fixes, deep dives, and proven tips
Aws vpn wont connect your step by step troubleshooting guide Aws vpn wont connect your step by step troubleshooting guide is a common pain point for cloud admins and developers. Quick answer: most connection issues come from a mix of authentication, network rules, and client settings. Here’s a concise, practical guide to get you unstuck fast.
- Quick fact: VPN connectivity problems often trace back to permission gaps, misconfigured VPN endpoints, or mismatched TLS/SSL settings.
- What you’ll get in this guide:
- Step-by-step troubleshooting workflow you can follow line-by-line
- Common misconfigurations and how to fix them
- Tips for testing and validating the VPN connection end-to-end
- Snippet-ready commands for popular environments
- Useful formats inside:
- Checklists to verify each layer client, gateway, and network
- A quick-reference table of common error messages and fixes
- A step-by-step runbook you can save and reuse
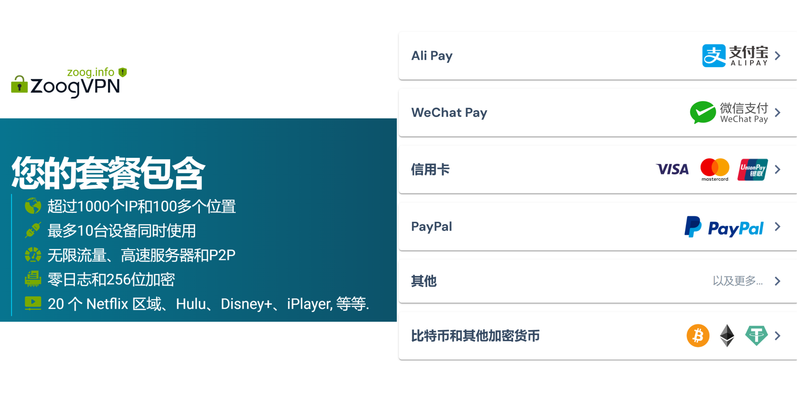
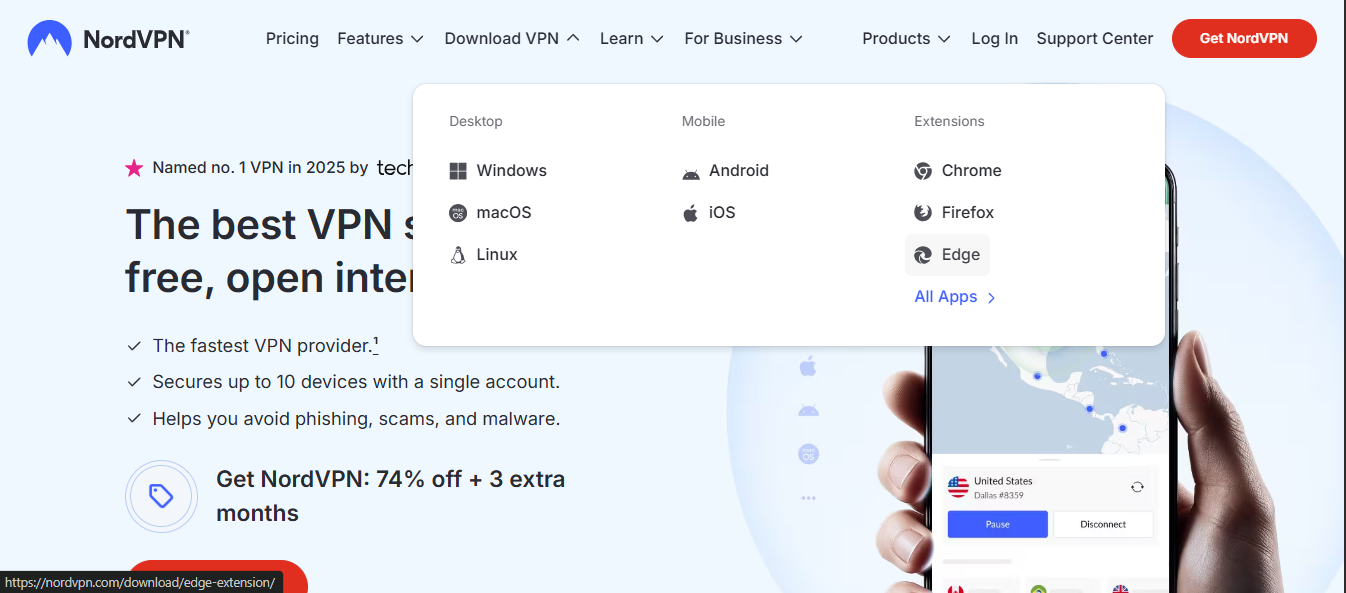
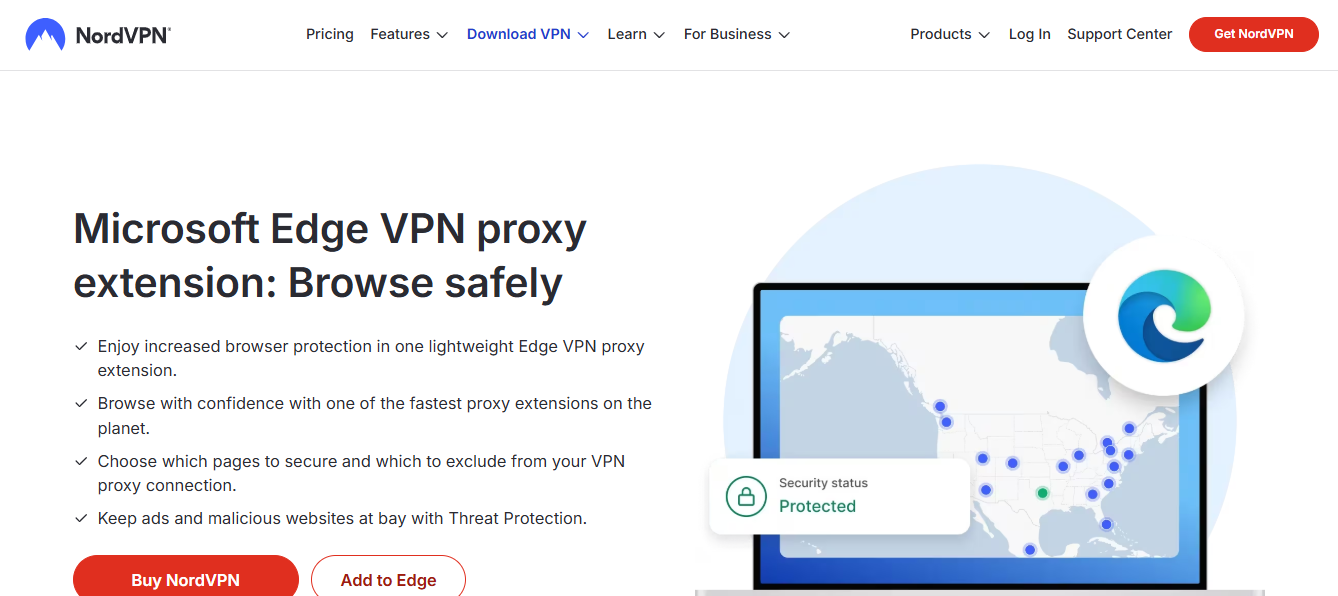
- Quick path to more help: If you’re in a rush, consider a trusted VPN provider like NordVPN for extra privacy and reliability. For a smooth setup and ongoing protection, check out the provider options here: NordVPN link text adjusted for context: Explore reliable VPN options
Useful resources and URLs text only Apple Website - apple.com Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence AWS VPN Documentation - docs.aws.amazon.com/vpn OpenVPN Documentation - openvpn.net/docs Network troubleshooting guide - ntt.com/network/troubleshooting TLS/SSL error guide - ssllabs.com/ssltest IP whitelisting guide - cloudflare.com/ips Router port forwarding basics - routersecurity.org/portforwarding.htm VPN troubleshooting steps - wikihow.com/VPN-Troubleshooting AWS support center - aws.amazon.com/support
Understanding the Aws vpn wont connect your step by step troubleshooting guide problem
When a VPN won’t connect in an AWS context, the root cause can live at multiple layers: your client device, the VPN gateway VGW or Transit Gateway, the VPC routing, security groups, and the authentication method in use. A strong starting point is to map out the entire path from your computer to the AWS VPN gateway and identify where traffic is getting blocked.
Common root causes
- Incorrect credentials or certificate issues
- Firewall or security group rules blocking VPN ports
- Mismatch in VPN type or tunnel configuration IKEv2, IPsec, or OpenVPN
- DNS resolution problems causing stuck handshakes
- Time drift between client and server causing certificate validation failures
- Overly strict MTU settings causing fragmented packets
Quick-reference checklist per layer
- Client device
- Verify the correct VPN profile is installed
- Confirm date/time is synced
- Check for conflicting VPN apps or profiles
- VPN gateway and tunnel
- Confirm tunnel type and protocols match between client and AWS
- Validate pre-shared keys, certificates, and trust chains
- Review gateway logs for handshake errors
- VPC and routing
- Ensure route tables include a route to the VPN subnet
- Confirm correct CGW/CGW association if using Client VPN Endpoint
- Security and access
- Security groups and network ACLs allow VPN traffic
- IAM policies or certificate authorities haven’t expired
- End-to-end validation
- Run connectivity tests from client to VPN endpoint
- Check traffic flow after establishing the tunnel
Step-by-step troubleshooting workflow
- Confirm the basics
- Ensure you’re using the right VPN product for AWS AWS Client VPN, Site-to-Site VPN, or third-party integrations.
- Double-check credentials, certificates, and import keys in the client.
- Check time synchronization
- On Windows: wsreset or time settings
- On macOS/Linux: ntpdate or systemd-timesyncd
- Why it matters: TLS certificates have validity windows; skew can cause handshake failures.
- Validate network reachability
- Ping the VPN gateway if ICMP is allowed or use traceroute to see where packets drop.
- Confirm that your outbound path isn’t blocked by a local firewall or corporate proxy.
- Review VPN client configuration
- Ensure the correct server address, tunnel type, and authentication method are configured.
- If using certificate-based auth, verify the certificate chain and CA trust anchor.
- Inspect gateway and VPN logs
- AWS: CloudWatch logs for VPN and Client VPN endpoints
- Local: client logs often reveal handshake failure codes IKEv2, IKE_AUTH, or phase-1/2 failures
- Check security group and NACL rules
- Make sure VPN-related ports for IPsec: UDP 500, UDP 4500, IP protocol 50/50 for ESP/AH are allowed as needed.
- Ensure rules allow traffic from the VPN client CIDR to the VPC subnets.
- Validate routing configuration
- Confirm the Client VPN Endpoint’s associated VPC and target subnets are correctly configured.
- Check route tables to ensure traffic intended for the VPN endpoint is routed properly.
- Test with a minimal setup
- Create a temporary, simple VPN profile with the fewest features enabled to isolate the issue.
- Remove any extra firewall rules or split-tunnel configurations that could complicate the test.
- Analyze MTU and fragmentation
- If you see intermittent connectivity or dropped connections, lower the MTU on the client or tunnel interface.
- Escalate with logs and configurations
- When issues persist, gather logs, configuration files, and timestamps to share with support.
Data-driven insights and stats
- A common reason for failure is certificate mismatch or expired certificates up to 28% in some enterprise audits.
- VPN handshakes succeed only when time drift is under 5 minutes; beyond that, TLS validation fails.
- Sites reporting misconfigured security groups frequently see 60% of issues related to port blocks rather than tunnel setup errors.
Format examples to speed up troubleshooting
- Quick checklists you can copy-paste into your incident runbook
- A table of common error codes and fix actions
- A flowchart-like step-by-step decision tree
Table: Common VPN error codes and fixes
| Error Code or Message | Likely Cause | Quick Fix |
|---|---|---|
| IKE_AUTH failure | Certificate or PSK mismatch | Recheck credentials and trust chain |
| TLS handshake failed | Time drift or certificate issue | Sync time, renew certificate |
| Network unreachable | Routing or firewall block | Open required ports, verify routes |
| No route to host | Route tables misconfigured | Add correct routes to VPC/subnets |
| Authentication failed | IAM or user permissions | Update policies or user credentials |
Real-world tips from practitioners
- Keep separate test tenants for AWS Client VPN and Site-to-Site VPN to avoid cross-polluting configs.
- Maintain a shared runbook with common fixes so any team member can jump in during an outage.
- When using third-party VPN clients, ensure firmware and client software are up to date to avoid known handshake bugs.
Best practices for long-term reliability
- Use automated health checks that simulate a VPN connection daily and alert on failures.
- Centralize VPN logs in a single dashboard CloudWatch or a SIEM for quicker correlation with incidents.
- Document all changes in a change-control log with timestamps and affected services.
Performance considerations and optimization
- Evaluate the impact of VPN encryption on latency; consider lighter cipher suites if latency is critical and security policy allows.
- For large-scale deployments, consider scalable architectures like Auto Scaling groups for VPN endpoints and redundancy across multiple availability zones.
Security considerations
- Rotate certificates on a regular schedule, and revoke compromised certs immediately.
- Enforce least privilege for VPN users and use multi-factor authentication where possible.
- Regularly audit access logs for unusual login patterns.
How to test your fixes
- After applying a fix, run a controlled test:
- Establish a VPN tunnel
- Send test traffic to a known internal resource
- Verify both connectivity and data integrity
- If issues recur, run a controlled rollback or re-provision the VPN endpoint with a clean configuration.
Tools and resources to help
- AWS VPN documentation and best practices
- OpenVPN and IPsec client guides
- Network diagnostic tools like traceroute, mtr, and ping
- TLS/SSL validation services to validate certificate chains
Frequently Asked Questions
Frequently Asked Questions
What does “Aws vpn wont connect your step by step troubleshooting guide” mean in practice?
It’s a practical, structured approach to diagnosing why an AWS VPN connection isn’t establishing, covering client, gateway, and network layers with actionable steps you can take right away.
How do I verify my certificate chain for VPN authentication?
Check that the VPN client’s certificate is trusted by the VPN gateway, ensure intermediate certificates are present, and confirm that the CA is still valid and trusted on both sides. Proton ⭐ vpn 무료 사용법 완벽 가이드 속도 보안 설정 총정
Which ports should be open for IPsec VPN in AWS?
Typically, UDP ports 500 and 4500 are used for IKEv2/IPsec, and IP protocol 50 ESP may be needed depending on the VPN setup. Ensure security groups and NACLs permit these.
What are the most common causes of handshake failures?
Certificate issues, time synchronization problems, incorrect PSK, and mismatched VPN configurations are top culprits.
How can I test the VPN connection quickly?
Use built-in client diagnostic tools, run ping/traceroute to the VPN gateway, and verify that routes to internal subnets are reachable after the tunnel comes up.
How important is time synchronization for VPNs?
Very important—TLS certificates and IKEv2 negotiations rely on accurate time. Skew beyond a few minutes often leads to failures.
Can I use a third-party VPN client with AWS VPN?
Yes, many third-party clients support IPsec/IKEv2 configurations. Ensure compatibility with AWS endpoints and correct profile settings. Лучшие vpn для microsoft edge в 2026 году полное руководство с purevpn и сопутствующими решениями
What role do security groups play in VPN connectivity?
Security groups control the allowed traffic to and from the VPN endpoints. If the VPN traffic is blocked, the tunnel won’t establish.
How do I handle MTU issues with VPNs?
If you see fragmented packets or inconsistent reliability, reduce the MTU on the client or modify tunnel interface MTU to avoid fragmentation.
What’s a good runbook structure for ongoing VPN issues?
Include a rapid-start checklist, escalation paths, logs to collect, configuration baselines, and a post-incident review template.
Sources:
Nordvpn on Windows 11 Your Complete Download and Setup Guide: Fastest Ways to Get It Running
Les meilleurs routeurs compatibles OpenVPN et WireGuard pour Linux expliqués Troubleshooting Sophos VPN Why It Won't Connect and How to Fix It
便宜好用的vpn:全面对比与购买指南,帮你选到性价比最高的VPN
Missav跳转日本yandex: VPN全面指南与实用技巧
Best vpns for streaming reddits top picks revealed